
What Is Incident Response and Why It Matters
South African engineering and financial firms regularly face challenges such as ransomware, phishing, and data breaches that threaten both business operations and compliance efforts. The reality is that every incident response misstep can lead to costly downtime, reputational harm, and regulatory penalties. Strengthening your organisation’s incident response strategy means protecting sensitive data, ensuring business continuity, and building lasting trust. This article unpacks what incident response really means in the context of South African cybersecurity, showing how the right approach helps reduce damage and supports compliance.
Key Takeaways
| Point | Details |
|---|---|
| Structured Incident Response is Essential | Incident response is vital for minimising damage and ensuring business continuity in the face of cyber threats. |
| Understanding Cybersecurity Threats is Crucial | Familiarity with various types of cyber incidents enables organisations to tailor their response strategies effectively. |
| Compliance is a Key Component | Adhering to legal requirements, such as the Cybercrimes Act and POPIA, is essential to avoid penalties and maintain stakeholder trust. |
| Regular Training and Simulations | Conducting frequent incident response exercises enhances team readiness and strengthens organisational resilience against cyber threats. |
Defining Incident Response in Cybersecurity
In the rapidly evolving digital landscape of South African businesses, incident response represents a structured, strategic approach to managing cybersecurity threats. Cybersecurity incident response involves a comprehensive set of activities designed to prepare for, detect, analyse, contain, and recover from potential digital security breaches.
At its core, incident response is about minimising damage and reducing recovery time when cyber threats emerge. This process encompasses several critical stages:
- Preparation: Establishing incident response policies and assembling response teams
- Detection and Analysis: Identifying potential security incidents and understanding their scope
- Containment: Limiting the spread and impact of the cybersecurity threat
- Eradication: Removing the threat from the organisation’s systems
- Recovery: Restoring systems and operations to normal functionality
For South African engineering and financial firms, incident response isn’t just a technical requirement – it’s a business survival strategy. Structured cybersecurity processes help organisations rapidly mitigate potential financial losses, protect sensitive data, and maintain operational continuity.

The following table outlines the unique challenges and benefits of incident response for South African businesses:
| Challenge | Example Impact | Strategic Benefit |
|---|---|---|
| Sophisticated cybercrime | Disruption of financial systems | Faster recovery limits financial loss |
| Regulatory pressures | Risk of hefty fines | Compliance builds business trust |
| High-profile breaches | Damage to corporate reputation | Robust response reassures stakeholders |
| Evolving threat landscape | Increased vulnerability | Preparedness reduces incident impact |
Effective incident response transforms potential catastrophic cyber events into manageable challenges that can be systematically addressed.
The complexity of modern cyber threats demands a proactive and comprehensive approach. Businesses must view incident response not as a reactive measure, but as an integral part of their overall risk management framework.
Pro tip: Regularly conduct simulated incident response exercises to test and refine your organisation’s cybersecurity readiness and team capabilities.
Types of Security Incidents in South Africa
South Africa’s digital landscape is increasingly vulnerable to a complex and evolving range of cybersecurity threats. Cybersecurity incidents in South Africa encompass a diverse array of malicious activities that target both public and private sector organisations, causing significant operational and financial disruptions.
The primary types of security incidents impacting South African businesses include:
- Phishing Attacks: Social engineering techniques designed to steal sensitive credentials
- Ransomware: Malicious software that encrypts organisational data and demands payment
- Data Breaches: Unauthorised access and extraction of confidential information
- Server Outages: Deliberate or accidental disruptions to critical IT infrastructure
- Identity Theft: Fraudulent impersonation using stolen personal or corporate information
- Denial of Service (DoS) Attacks: Overwhelming systems to render them non-functional
South African cyber incidents have demonstrated significant real-world impact, with recent examples including ransomware attacks disrupting health services and sophisticated breaches targeting mining company IT systems. These incidents highlight the critical need for robust cybersecurity strategies across all sectors.
Cybersecurity is no longer optional – it’s a fundamental business survival requirement in the digital age.
Understanding these threat types is crucial for developing comprehensive incident response strategies. Each incident type requires specific detection, containment, and recovery approaches tailored to its unique characteristics.
Pro tip: Conduct regular cybersecurity threat assessments and maintain updated incident response playbooks specific to the most prevalent threats in the South African business ecosystem.
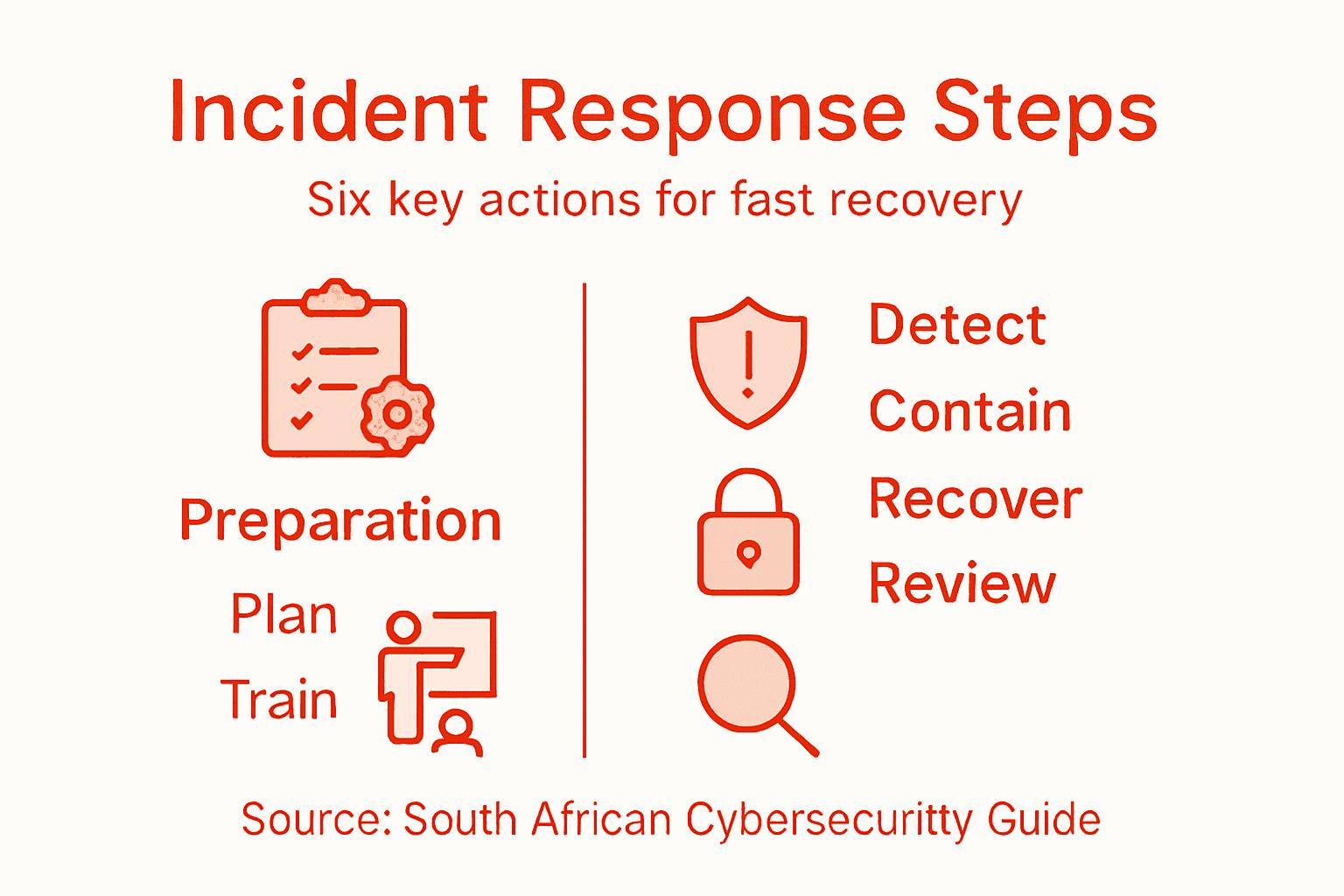
Key Steps in the Incident Response Process
Navigating a cybersecurity incident requires a structured and methodical approach that minimises potential damage and accelerates recovery. Incident reporting procedures provide a critical framework for organisations to manage and mitigate digital security threats effectively.
The incident response process typically involves several key strategic steps:
- Preparation Phase
- Develop comprehensive incident response policies
- Establish dedicated response teams
- Create communication protocols
- Implement monitoring and detection systems
- Detection and Identification
- Recognise potential security breaches
- Collect initial evidence
- Assess the scope and potential impact
- Containment
- Isolate affected systems
- Prevent further spread of the incident
- Preserve forensic evidence
- Eradication
- Remove the threat from systems
- Patch vulnerabilities
- Clean infected infrastructure
- Recovery
- Restore systems to normal operation
- Verify system integrity
- Implement additional security measures
Comprehensive incident investigation requires meticulous documentation, witness interviews, and thorough analysis of root causes. South African organisations must ensure these processes comply with local regulatory standards and best practices.
Effective incident response is not just about technical resolution, but about understanding and preventing future vulnerabilities.
Successful incident management demands a proactive, well-coordinated approach that integrates technical expertise with strategic thinking. Each step must be executed with precision and care to minimise potential business disruption.
Pro tip: Develop and regularly update a detailed incident response playbook that includes specific procedures for different types of cybersecurity threats.
Roles and Responsibilities for IT Teams
In the complex landscape of cybersecurity incident response, IT teams play a pivotal role in safeguarding organisational digital infrastructure. Cybersecurity professional responsibilities extend far beyond traditional technical management, encompassing strategic risk mitigation and regulatory compliance.
The key roles within incident response teams include:
-
Incident Response Coordinator
- Lead overall incident management strategy
- Coordinate cross-functional response efforts
- Communicate with senior management
-
Security Analyst
- Monitor network and system activities
- Detect potential security breaches
- Conduct initial threat assessments
-
Forensic Investigator
- Collect and preserve digital evidence
- Perform detailed technical investigations
- Document incident chronology and impact
-
Technical Recovery Specialist
- Develop system restoration protocols
- Implement recovery strategies
- Verify system integrity post-incident
Cybersecurity legal obligations require IT professionals to maintain rigorous standards of system protection and incident reporting. These responsibilities demand a comprehensive understanding of both technical complexities and regulatory frameworks specific to South African business environments.
Effective incident response is a team sport – no single role can manage cybersecurity challenges alone.
Successful incident response teams require a diverse skill set, combining technical expertise, strategic thinking, and collaborative problem-solving. Each team member must understand their specific responsibilities while maintaining a holistic view of organisational cybersecurity.
Pro tip: Develop comprehensive cross-training programs that enable team members to understand multiple incident response roles and enhance overall team resilience.
Compliance, Legal, and Financial Implications
In the complex South African business landscape, cybersecurity incident response extends far beyond technical management, encompassing critical legal and financial dimensions. Cybersecurity legislation imposes stringent requirements that organisations must navigate to protect their digital assets and maintain regulatory compliance.
Key legal and financial implications for South African businesses include:
-
Regulatory Penalties
- Fines up to R50 million or 10% of annual turnover
- Potential criminal prosecution for non-compliance
- Mandatory incident reporting within specified timeframes
-
Financial Risk Exposure
- Direct costs of system restoration
- Potential litigation expenses
- Reputation damage and lost business opportunities
- Potential insurance premium increases
-
Compliance Requirements
- Adherence to Cybercrimes Act of 2020
- Compliance with Protection of Personal Information Act (POPIA)
- Implementation of robust risk management frameworks
Risk management compliance demands a proactive approach to identifying, assessing, and mitigating potential cybersecurity vulnerabilities. South African organisations must develop comprehensive strategies that align technical capabilities with legal obligations.
Effective incident response is not just a technical challenge, but a critical business survival strategy.
Beyond immediate financial implications, non-compliance can trigger cascading consequences including regulatory sanctions, loss of business licenses, and permanent reputational damage. Organisations must view incident response as a strategic investment in organisational resilience.
Here is a summary of regulatory requirements relevant to cybersecurity incident response in South Africa:
| Regulation | Primary Objective | Key Obligation |
|---|---|---|
| Cybercrimes Act 2020 | Combat cyber-enabled crime | Mandatory incident reporting |
| POPIA | Protect personal information | Data breach notification |
| Regulatory Penalty Limits | Enforce compliance through penalties | Fines and legal prosecution |
| Risk Management Framework | Guide ongoing organisational review | Regular compliance audits |
Pro tip: Conduct regular compliance audits and maintain detailed documentation of incident response procedures to demonstrate proactive risk management to regulators and stakeholders.
Strengthen Your Incident Response with Expert IT Support
Protecting your business against cyber threats requires more than just understanding incident response It demands proactive strategies that minimise damage and ensure swift recovery South African engineering and financial firms face sophisticated cybercrime, regulatory pressures, and reputational risks every day Techtron specialises in offering fully managed and co-managed IT services designed to enhance your cybersecurity posture and incident handling capabilities
Our comprehensive solutions include network security, backup and disaster recovery, and cloud services like Microsoft 365 and Azure We focus on reducing your technical burdens while helping you maintain compliance and operational continuity When rapid detection and containment matter most, partnering with a trusted IT provider allows your business to respond effectively to emerging cyber incidents Visit Techtron to explore how our tailored IT management services can protect your digital assets and prepare your team for any security challenge Don’t wait for an incident to expose vulnerabilities Act now and secure your business resilience with expert IT support that understands the critical importance of incident response
Frequently Asked Questions
What is incident response in cybersecurity?
Incident response in cybersecurity is a structured approach for managing security breaches or threats. It involves preparing for, detecting, analyzing, containing, and recovering from potential digital security incidents to minimize damage and ensure business continuity.
Why is incident response important for businesses?
Incident response is vital for businesses as it helps to quickly mitigate financial losses, protect sensitive data, maintain operational continuity, and build trust with stakeholders by demonstrating a commitment to cybersecurity.
What are the key steps in the incident response process?
The key steps in the incident response process include preparation, detection and identification, containment, eradication, and recovery. Each step is crucial for effectively managing a cybersecurity incident and minimizing its impact on the organization.
Who is involved in an incident response team?
An incident response team typically includes an Incident Response Coordinator, Security Analysts, Forensic Investigators, and Technical Recovery Specialists. Each role contributes specific expertise to ensure a comprehensive and effective response to cybersecurity incidents.
Recommended
- Understanding IT Risk Management Strategies for Businesses – TECHTRON
- Understanding Disaster Recovery Planning for Businesses – TECHTRON
- Understanding the IT Risk Assessment Process – TECHTRON
- Understanding Business Continuity Strategies for Resilience – TECHTRON
- How to assess lightning risks for a site or infrastructure? – Lightning Protection Systems France – Lightning Protection